Mixed Entry Verification – qarovviraf153, iieziazjaqix4.9.5.5, Flapttimzaq, zimslapt2154, Rozunonzahon
Mixed Entry Verification, as framed by qarovviraf153, iieziazjaqix4.9.5.5, Flapttimzaq, zimslapt2154, and Rozunonzahon, presents a disciplined approach to assembling, recording, and tracing blended inputs. The discussion centers on authenticating sources, detecting anomalies, and enforcing verifiable workflows that render each component auditable. The approach relies on consistent labeling, metadata, and ownership to ensure reproducibility. A precise evaluation of tools and metrics is essential to determine where improvements are warranted and how risks are mitigated as processes scale.
What Mixed Entry Verification Is and Why It Matters
Mixed Entry Verification refers to the process of confirming that a blend or combination of inputs—such as data sources, samples, or components—has been accurately assembled and recorded, ensuring that each element is correctly represented and traceable within the final dataset or product.
The discussion outlines mixed entry concepts, verification workflow steps, anomaly detection signals, authentication safeguards, best practices, pitfalls, tools evaluation, and effectiveness metrics.
Core Components: Authentication, Anomaly Detection, and Verification Workflows
This section delineates three core components—authentication, anomaly detection, and verification workflows—whose integration underpins reliable mixed-entry verification.
The discussion adopts a methodical lens, detailing mechanisms, data signals, and decision criteria.
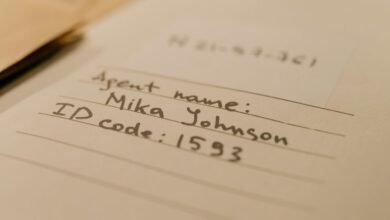
It surveys evidence-based approaches for Mixed entry authentication and clarifies how Verification workflows coordinate checks, approvals, and audit trails, enabling transparent, flexible governance within independent yet coordinated systems.
Implementing Mixed Entry Verification: Best Practices and Pitfalls
Implementing mixed entry verification requires a structured approach that translates the previously outlined components—authentication, anomaly detection, and verification workflows—into actionable practices. The methodical framework emphasizes risk-aware sequencing, clear ownership, and continuous refinement. Practitioners document assumptions, monitor deviations, and adjust thresholds. When executed rigorously, mixed entry enhances reliability, reduces false positives, and strengthens verification workflows without sacrificing agility or user autonomy.
Evaluating Tools and Metrics to Measure Effectiveness
Evaluating tools and metrics to measure effectiveness requires a disciplined, evidence-based approach that pairs objective performance indicators with operational context. The analysis focuses on mixed entry verification metrics, applying standardized benchmarks and transparent data collection. Detachment enables objective comparison across methods, revealing gaps and tradeoffs. Results guide iterative refinement, emphasizing reproducibility, auditability, and freedom-friendly criteria for sustained improvement.
Conclusion
Mixed entry verification integrates authentication, anomaly detection, and verified workflows to ensure traceability and accountability across complex inputs. By aligning metadata, ownership, and auditable records, it supports reproducibility and continuous improvement. Implementations should emphasize risk-aware sequencing and transparent labeling to reduce errors and enhance trust. Are the prevailing controls consistently applied across all stages, and how quickly can anomalies trigger corrective actions to preserve data integrity? In sum, a disciplined, evidence-based approach yields reliable, auditable outcomes.